
What’s New (Updated about CMMC Final Rule)
Right now, following the release of the CMMC Final Rule and the start of enforcement on November 10, 2025, this blog has been updated to reflect the now-active assessment requirements, subcontractor flow-down obligations, and the need for contractors to prepare for Level 1 or Level 2 compliance at contract award. As as result, all forward-looking statements about when CMMC “will arrive” have been updated to reflect its current enforceable status.
Cybersecurity Maturity Modification Certification Has Arrived and Is Now a Real Thing
At this point, think of CMMC as a train that has now arrived. In other words, the best move is to be fully compliant. As a result, for organizations in the Defense Industrial Base (DIB), the choice is simple: stay compliant or risk being left behind at contract award.
Why now? On July 22, the Department of Defense (DoD) sent its proposed final language for Title 48 of the Code of Federal Regulations (CFR 48) to the Office of Management and Budget’s (OMB) Office of Information and Regulatory Affairs (OIRA) for review. As a result, with the Final Rule active as of November 10, 2025, CMMC is now official and already appearing in DoD contract solicitations.
From DFARS 7012 to CMMC 2.0: How We Got Here
To put this in context, a bit of historical context helps put the current status into perspective. For nearly a decade, DIB companies that send, receive, store, process, or otherwise handle controlled unclassified information (CUI) have been required to meet the 110 security controls defined in National Institute of Standards and Technology Special Publication 800-171 (NIST SP 800-171). Defense Federal Acquisition Regulation Supplement (DFARS) clause 252.204-7012 (DFARS 7012) codifies that mandate.
Historically, DFARS 7012 allowed organizations to self-assess and self-report their compliance with NIST SP 800-171. In practice, however, many businesses fell short by:
- Not attesting their compliance in the DoD’s Supplier Performance Risk System (SPRS)
- Misjudging or incorrectly calculating their compliance score
- Failing to complete their Plans of Action and Milestones (POA&Ms) to close security gaps
These shortcomings created risk for the DIB, triggering huge financial losses1 and elevating threats to national security to unacceptable levels.
Why Self-Attestation Failed and CMMC Was Created
Ultimately, the DFARS 7012 self-assessment approach did not work as intended. In response, the DoD changed course and initiated CMMC to better protect CUI and federal contract information (FCI). CMMC brings a critical change: most DIB firms will no longer be able to self-assess and self-report their compliance with NIST SP 800-171. Instead, going forward, they will only receive CMMC accreditation after passing an audit conducted by an approved CMMC 3rd Party Assessment Organization (C3PAO).
After that, in December 2024, the DoD completed the process of formally defining CMMC with the publication of Title 32 of the CFR in the Federal Register. CMMC 2.0 comprises three maturity levels, with nearly all the DIB falling within Level 1 and Level 2.
- CMMC Level 1 encompasses 17 controls from NIST SP 800-171 to protect FCI and allows companies to self-assess and self-attest compliance.
- CMMC Level 2 encompasses all 110 controls from NIST SP 800-171 Revision 2 to protect FCI and CUI and requires (with a small percentage of exceptions) organizations to pass a C3PAO audit to become accredited.
- CMMC Level 3 encompasses 110 controls from NIST SP 800-171 plus an additional 24 controls from NIST SP 800-172 to account for advanced persistent threats. The Defense Contract Management Agency’s (DCMA) Defense Industrial Base Cybersecurity Assessment Center (DIBCAC) conducts the assessment for accreditation.
At this stage, CMMC 2.0 is now fully enforceable. With the publication of the Final Rule and activation of DFARS 7021 through updated Federal Register processes, contracting officers may include CMMC Level 1 or Level 2 requirements in solicitations, and contractors must meet the specified level at contract award.
CMMC-Related Acronyms You Need to Know and Why They Matter
Key Terms and Acronyms Used in CMMC
| Acronym | Definition | Why It’s Important |
| CMMC | Cybersecurity Maturity Model Certification | DoD’s framework to ensure contractors protect Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) through verified cybersecurity practices. Required for winning future DoD contracts. |
| CUI | Controlled Unclassified Information | Sensitive government data that is not classified but requires safeguarding. Loss of CUI can lead to financial harm and national security risks. |
| FCI | Federal Contract Information | Information provided by or generated for the government under a contract, not intended for public release. Protecting FCI is the foundation of CMMC Level 1 compliance. |
| DFARS | Defense Federal Acquisition Regulation Supplement | DoD-specific acquisition rules. Clauses like 7012 and 7021 define cybersecurity requirements and enforcement mechanisms for defense contractors. |
| DFARS 7012 | DFARS Clause 252.204-7012 | Requires contractors to implement NIST SP 800-171 and report cyber incidents, historically allowing self-assessment. The starting point for today’s CMMC requirements. |
| DFARS 7021 | DFARS Clause 252.204-7021 | Activates CMMC requirements in DoD contracts, making third-party certification mandatory for certain levels. |
| NIST SP 800-171 | National Institute of Standards and Technology Special Publication 800-171 | Defines 110 security controls for protecting CUI in nonfederal systems, the backbone of CMMC Level 2 compliance. |
| POA&M | Plan of Action and Milestones | A documented plan for addressing cybersecurity gaps. In CMMC, incomplete POA&Ms can delay certification. |
| SSP | System Security Plan | Detailed documentation describing how an organization implements NIST SP 800-171 controls. A key requirement for passing a C3PAO audit. |
| SPRS | Supplier Performance Risk System | DoD’s platform for submitting and storing cybersecurity self-assessment scores. Critical for demonstrating compliance readiness under DFARS 7012. |
| C3PAO | CMMC Third-Party Assessment Organization | Authorized entities that conduct CMMC Level 2 and above audits. Limited availability means scheduling early is essential. |
| OIRA | Office of Information and Regulatory Affairs | Federal office that reviews and approves new rules like CFR 48 before they are published and enforced. |
| CFR | Code of Federal Regulations | The codified rules and regulations of federal agencies. Title 32 and Title 48 define and implement CMMC requirements. |
How These Acronyms Affect Your CMMC Readiness
Understanding these terms helps contractors interpret solicitations, assessments, and documentation requirements more accurately.
What Happens Next? The Final Steps Before CMMC 2.0 Arrives
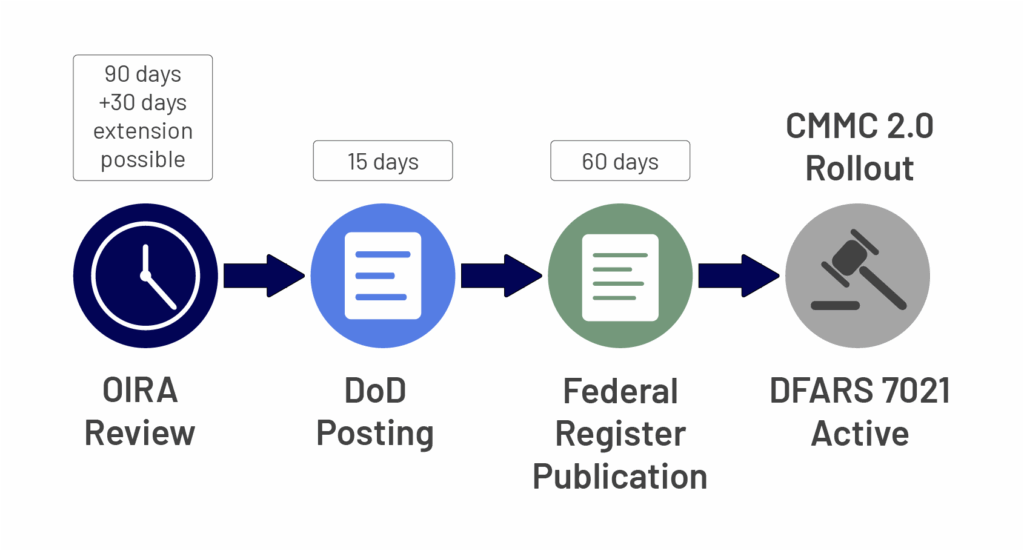
At this point, with CFR 48 now in the hands of OMB’s OIRA, the timeline for what happens next becomes much clearer. CFR 48, with the option to request a 30-day extension. Upon OIRA approval, the DoD has 15 days to post CFR 48 to the Federal Register. As a result, publication on the Federal Register triggers a 60-day period for Congress or the President to raise any objections, after which DFARS 7021 becomes active and the CMMC 2.0 rollout begins.
What the CFR 48 Timeline Means for Contractors
So, what does this mean realistically in terms of timing? The CMMC train will likely arrive at its final destination sometime in the fourth quarter of this year, especially in light of Defense Secretary Hegseth’s recent memo explicitly identifying the importance of CMMC to protect DoD assets from foreign access.
For comparison, OIRA took close to the full 90 days to review and approve CFR 32, a far more complex rule than CFR 48. If they follow the same track, the DoD uses its full 15 days to post the rule, and Congress and the President remain silent for all 60 days, DFARS 7021 goes live near the end of Q4. If OIRA and the DoD move more quickly and Congress and the President forfeit their rights to object prior to the close of their 60-day window (a distinct possibility given that CFR 48 has been deemed economically insignificant), DFARS 7021 takes effect near the beginning of Q4.
Why Get CMMC Ready Now? The Numbers Tell the Story
As of now, CFR 448 is complete, even the strongest skeptics must admit that CMMC requirements are already appearing in new DoD contract solicitations, and contractors must be prepared to meet Level 1 or Level 2 requirements at award.
CMMC 2.0 is now in an active enforcement phase through the Final Rule’s implementation framework.
How Long Will CMMC Prep Really Take?
In many cases, even organizations with strong security processes, procedures, and personnel will need up to six months to assess themselves accurately versus NIST SP 800-171’s 110 controls, address shortcomings, and gather and produce required documentation, including System Security Plans (SSPs). Others may require 12 or perhaps as many as 18 months to do so, depending on the size and scope of their enterprise and their current degree of security maturity.
As a rule, getting ready takes longer than you think, especially when you will be assessed by a C3PAO and want to pass and gain accreditation on the first try (failing adds significant time and cost to an already expensive and lengthy process).
In addition, don’t underestimate the time to schedule a C3PAO audit. At the same time, demand for CMMC Level 2 Certification will be high, with around 70,000 DIB organizations seeking accreditation and fewer than 80 C3PAOs authorized to perform the audits. While that number is steadily growing, scheduling will take time. As such, the good news is that organizations that start early and get on a C3PAO’s calendar now will avoid long waits down the road. By planning ahead, you’ll keep your certification process on track and position your business to compete for contracts as soon as requirements appear.
- 6 months – Time even mature organizations need to prepare for an audit
- 12–18 months – Prep time for less mature organizations
- ~70,000 DIBs vs <80 auditors – Organizations competing for limited C3PAO availability
- Failing the first audit adds cost, delays, and could mean lost contracts
In the meantime, the DoD will start issuing contract solicitations that require CMMC soon. So, if you don’t have the accreditation, you won’t win or be on the winning team. Period. Can your business risk the potential loss of revenue?
Accelerate Your CMMC Compliance Journey with Exostar’s CMMC Ready Suite
At the same time, CMMC crunch time has arrived. Exostar offers cost-effective resources to help prepare for CMMC accreditation, so you maintain the competitive advantage that keeps DoD revenue opportunities in play. Exostar’s CMMC Ready Suite includes:
- Exostar’s Managed Microsoft 365 – A fully-managed enclave for secure and compliant external and internal management and sharing of FCI, CUI, and other sensitive information and intellectual property that meets 85 of the 110 NIST SP 800-171 controls out of the box.
- Certification Assistant – A product that helps you understand the NIST SP 800-171 controls, guides and tracks your self-assessment progress, archives important information for C3PAO assessment, creates the SSP and POA&Ms, and accurately computes your assessment score for upload to SPRS.
- Exostar PolicyPro – A product that leverages artificial intelligence to create policies defined in NIST SP 800-171 compliantly from scratch or from existing policies by identifying and remediating shortcomings.
If so, and you need help assessing your documentation, centralizing evidence, or preparing for Level 1 or Level 2 assessments, explore structured solutions designed to support readiness under the active CMMC Final Rule.
What You Should Do Now
To begin with, contractors should review their SSP, confirm SPRS scoring accuracy, ensure DFARS flow-down requirements are reflected in all subcontractor agreement. Plus, they should determine whether their upcoming solicitations require a Level 1 self-assessment or a Level 2 C3PAO certification. Also, the CMMC Levels Quiz can help identify your correct level under the Final Rule.
Revised December 5,2025
1 “Raytheon Companies and Nightwing Group to Pay $8.4M to Resolve False Claims Act Allegations Relating to Non-Compliance with Cybersecurity Requirements in Federal Contracts,” Office of Public Affairs, U.S. Department of Justice.
